[ad_1]


Revealed: October 02, 2023 at 9:07 am Up to date: October 02, 2023 at 9:07 am

Edited and fact-checked:
In Transient
On this information, we delve into the highest 10 darknet browsers of 2023, evaluating their privateness, safety, and user-friendliness.
Web customers can surf the darkish internet anonymously due to specialised darknet browsers. The darkish internet helps anonymity and free speech, however it additionally hosts unlawful and immoral content material.
This text goals to present an intensive evaluation of the highest ten darknet browsers for 2023, ranking them in keeping with privateness, safety, and usefulness requirements. We’ll go into nice element about the advantages and disadvantages of every browser, supported by a helpful comparability desk.

Unveiling the Enigma: The Darkish Net and Darknet
The phrase “darkish internet” refers to a area of internet sites and content material discovered on overlay networks referred to as darknets, to which entry requires specific software program, setups, or authorization. By way of using onion routing and lots of layers of encryption to hide customers’ names and places, darknets present secret and nameless communication.
Key Illuminations in regards to the darkish internet
Accessible solely by darknet browsers like Tor or I2P, using distinctive routing protocols.Acknowledged as a hub for illegal pursuits resembling illicit drug markets and cyber intrusions.Additionally homes reliable endeavors resembling whistleblowing and expressions of dissent in oppressive regimes.Facilitates hid discourse, thereby safeguarding privateness, but concurrently harboring potential for illicit actions.
Nonetheless, it’s crucial to acknowledge that the darkish internet can be a realm the place some customers interact for illegitimate or unscrupulous functions:
Cybercrime Markets: Darknet markets facilitate the illicit commerce of narcotics, weaponry, and contraband.Hacking and Malware: Darknets disseminate instruments for hacking, malware, and the purloined information or credentials.Monetary Malfeasance: The darkish internet turns into a hub for identification theft, tax evasion, and cash laundering.Terrorism: Encrypted channels inside the darkish internet can facilitate terrorist actions.
Right here, we offer the highest ten darknet browsers of 2023, which have been rigorously in comparison with business requirements for privateness, safety, and usefulness.
1. Tor Browser
The Tor browser stands because the venerable luminary of darknet browsers, leveraging onion routing and encryption for unparalleled anonymity. Developed beneath the aegis of the non-profit Tor venture, with sponsorship from the U.S. authorities and varied organizations.
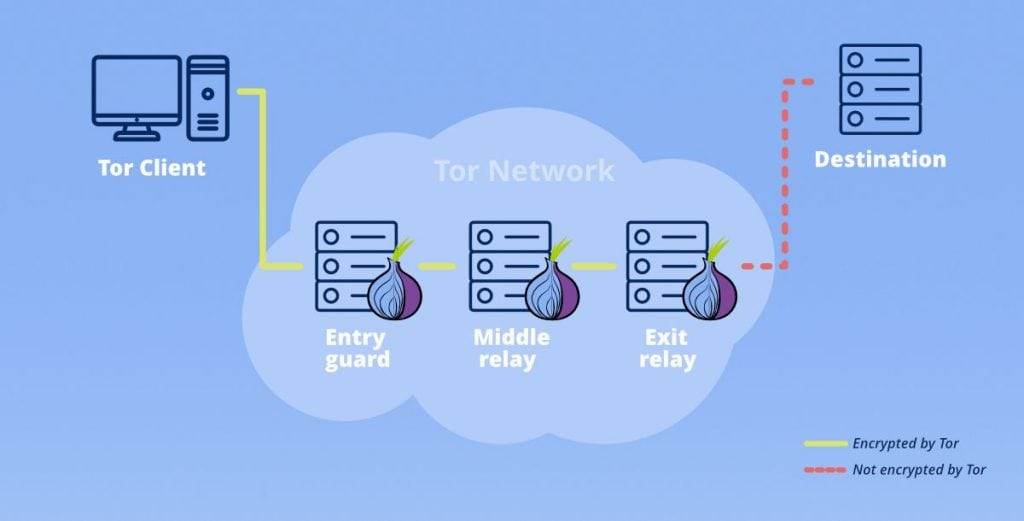
Privateness: Tor veils person IP addresses and places by channeling site visitors by a worldwide community of encrypted tunnels overseen by a legion of volunteer nodes. This yields an exalted stage of anonymity, rendering person actions practically untraceable.
Safety: The presence of encrypted tunnels and steady IP rotation bolsters defenses in opposition to surveillance and monitoring. Visitors undergoes a number of layers of encryption, thwarting interception and monitoring makes an attempt. The community reveals resilience even within the face of node compromise.
Consumer Expertise: The method of downloading and configuring Tor is comparatively simple. Its person interface, resembling Firefox ESR, supplies a well-recognized gateway to darkish web pages using the .onion area. A thriving person neighborhood augments the provision of complete documentation and assist.
Key Options:
Onion routing conceals IP and site.Zero logging of community exercise.Entry to .onion-ending darkish web pages.Built-in bridge relays in censored areas.In-built VPN and fingerprinting safety.
Limitations:
Looking velocity could endure as a result of routing encryption.Potential publicity to unencrypted information by way of malicious exit nodes.Some mainstream web sites endeavor to dam Tor entry.
2. I2P
I2P, also called the Invisible Web Undertaking, stands as a formidable darknet browser akin to Tor. It employs garlic routing and encryption, with darkish web pages denoted by the .i2p suffix.
Privateness: I2P shepherds site visitors by a decentralized peer-to-peer community, fortified with layered encryption, confounding efforts to hint actions. Each side of I2P’s operation is shrouded in end-to-end encryption, even community database inquiries.
Safety: I2P channels make use of end-to-end encryption for all site visitors. The community database is dispersed throughout nodes and shielded with encryption. Imperviousness to adversarial forces is a paramount goal.
Consumer Expertise: Organising I2P proves to be extra intricate in comparison with Tor, and its person interface, whereas practical, lacks the user-friendly polish of Tor. Documentation leans in direction of the technical.
Key Options:
Garlic routing mechanism for anonymity.Completely decentralized peer-to-peer community structure.Hid .i2p web sites and companies.Pervasive end-to-end encrypted tunnels.
Limitations:
In varied eventualities, I2P reveals slower efficiency in comparison with Tor.The worldwide peer community of I2P pales compared to Tor.A steeper studying curve accompanies I2P utilization.
3. Courageous Browser
Courageous, an open-source Chromium-based internet browser, locations a pronounced emphasis on privateness. It incorporates an non-obligatory built-in Tor tab for clandestine shopping periods.
Privateness: By default, Courageous staunchly blocks trackers and ads throughout standard shopping. The Tor tab funnels site visitors by the Tor community, heightening anonymity throughout delicate shopping periods.
Safety: Courageous boasts strong security measures, resembling common HTTPS enforcement. The mixing of Tor introduces an extra layer of encryption when activated.
Consumer Expertise: Sporting a user-friendly interface paying homage to Chrome, Courageous makes enabling the Tor personal tab by way of settings for expedited nameless shopping easy.
Key Options:
Tor Non-public Tabs seamlessly combine Tor routing.Default blocking of trackers and ads.Inclusion of HTTPS In every single place encryption extension.Optionally available Courageous Rewards system for contributing to web sites.
Limitations:
Superior configuration choices for Tor are absent.Restricted isolation between Tor and non-Tor shopping.Shares the identical browser profile, posing potential privateness dangers.
4. Opera Browser
Opera, a broadly embraced, multi-platform internet browser, encompasses a built-in VPN service. It extends partial capabilities for darkish internet entry by way of its VPN.
Privateness: The native Opera VPN conceals your IP handle by funneling site visitors by distant servers, amplifying anonymity. Customers possess the freedom to pick VPN server places, additional obfuscating their on-line presence.
Safety: VPN encryption safeguards site visitors in opposition to surveillance and monitoring. No information of exercise or connections are maintained.
Consumer Expertise: Activating the built-in VPN is a breeze, requiring a easy click on. Nonetheless, the choices for configuring VPN servers are considerably restricted.
Key Options:
An included, boundless VPN service.Entry to over 2,000 VPN server places worldwide.Employment of sturdy 256-bit AES encryption.Absence of exercise or site visitors logging.
Limitations:
VPN safety could also be thought of inferior to Tor’s encryption.Opera’s VPN community encompasses fewer servers than paid companies.Possession of distant servers pertains to the VPN firm.
5. Epic Browser
Epic Browser, staunchly dedicated to privateness, integrates built-in proxy assist. It facilitates entry to pick darkish internet content material by international proxy servers.
Privateness: Epic can channel site visitors by proxy servers dispersed throughout various continents, concealing the person’s IP handle. Whereas this furnishes a modicum of anonymity, it falls in need of Tor or VPN requirements.
Safety: Encryption stands because the bulwark between the browser and proxy servers, fortifying site visitors in opposition to surveillance and information assortment.
Consumer Expertise: Activating proxy assist and choosing server places proves to be remarkably simple, with a clear and user-friendly interface.
Key Options:
Seamless integration of proxy servers.Easy proxy activation with a single click on.Empowerment to decide on proxy server places.Efficient blockade of trackers and ads.Absence of person exercise logging.
Limitations:
Proxy server choices are exceedingly restricted.Proxies are much less safe than Tor or VPNs.Lack of .onion routing capabilities.
6. GNU IceCat
GNU IceCat stands as a modified Firefox browser devoted to privateness and freedom, birthed from the GNU open-source venture.
Privateness: IceCat excels in disabling analytics companies and telemetry that transmit information to Mozilla. These modifications elevate privateness requirements past these provided by commonplace Firefox.
Safety: IceCat builds upon Firefox’s strong safety structure, probably incorporating extensions resembling Tor for encryption.
Consumer Expertise: Boasting an interface practically indistinguishable from Firefox, IceCat supplies a way of familiarity. Nonetheless, the setup of privateness extensions necessitates a level of effort.
Key Options:
Disabling of analytics and monitoring companies.Clear, open-source code.Compatibility with main add-ons like Tor and VPN.Liberation from copyright constraints and DRM.
Limitations:
Handbook setup is obligatory for VPN and Tor extensions.Lacks built-in darkish internet routing capabilities.Enjoys lesser recognition and a smaller neighborhood in comparison with Tor.
7. Comodo Dragon
Comodo Dragon, grounded in Chromium, is a browser devoted to safety and privateness. It incorporates capabilities for darkish internet entry by extensions.
Privateness: It excels in blocking ads, trackers, and malicious web sites. Privateness settings allow the disabling of knowledge sharing.
Safety: Comodo Dragon adopts container isolation to mitigate harm within the occasion of malware publicity. The browser additionally boasts strong antivirus capabilities.
Consumer Expertise: Familiarity abounds within the Chrome-like interface. Nonetheless, darkish internet entry mandates the set up of extensions resembling Tor.
Key Options:
Effectual blocking of ads, trackers, and malicious web sites.Containers that isolate and mitigate the impression of malware.Privateness settings that stymie information assortment.Compatibility with VPN and Tor extensions.
Limitations:
Counting on add-ons for darkish internet entry.The browser’s closed-source nature limits transparency.Possession ties to an promoting firm.
8. SRWare Iron
SRWare Iron, one other Chromium-based browser ardently centered on privateness, eliminates Google monitoring companies and UI modifications.
Privateness: It eradicates Google companies resembling Google Analytics, crash reporting, and spell-checking. Information transmission to Google is tightly curtailed, imbuing a way of transparency.
Safety: Whereas retaining the core safety mannequin of Chromium, SRWare Iron incorporates advert and script blockers for heightened safety.
Consumer Expertise: The interface, practically equivalent to Chrome, grants customers a way of familiarity. Nonetheless, the journey to darkish internet entry necessitates the set up of extensions.
Key Options:
Removing of Google companies and modifications.Choices for blocking scripts and ads.Plentiful superior privateness configuration selections.Compatibility with Tor and VPN extensions.
Limitations:
Dependency on plugins for darkish internet entry.A much less celebrated browser with a smaller person neighborhood.Continues to lean on the Chromium engine.
9. Waterfox

Waterfox, an open-source browser constructed on the foundations of Firefox, prioritizes privateness. It excises Mozilla’s analytics companies.
Privateness: Waterfox disables telemetry, analytics, and Home windows information assortment companies, considerably diminishing information despatched to Mozilla.
Safety: Leveraging Firefox’s present safety framework, Waterfox can incorporate extensions for encryption.
Consumer Expertise: The interface mirrors Firefox carefully. Nonetheless, configuring VPN or Tor necessitates a level of guide setup.
Key Options:
Elimination of analytics and monitoring companies.Enhanced efficiency optimization.A longtime codebase rooted in Firefox.Compatibility with main privateness extensions.
Limitations:
Handbook setup is obligatory for darkish internet entry.A smaller neighborhood in comparison with Firefox and Tor.Not completely designed for darkish internet utilization.
10. Darknet Proxy
Darknet Proxy, an uncomplicated Tor proxy website, affords entry to the darkish internet with out requiring set up.
Privateness: It cloaks your IP handle by directing site visitors by the Tor community, furnishing a modicum of anonymity. Nonetheless, shopper encryption is conspicuously absent.
Safety: The service depends totally on Tor community encryption and lacks client-side encryption and isolation.
Consumer Expertise: No set up is required; merely load the web page and begin shopping. Nonetheless, customization choices stay restricted.
Key Options:
An easy web-based Tor proxy.Zero set up conditions.Swift entry to darkish web sites.A smattering of customization selections.
Limitations:
The function set is exceedingly sparse in comparison with the excellent Tor Browser.There exists a threat of website discontinuation or closure.Absence of client-side safety and isolation.
The Darknet Browser Panorama: A Comparative Evaluation
Darknet Browser FAQs
Is Darkish Net Entry Authorized?
Accessing the darkish internet shouldn’t be unlawful in and of itself. Alternatively, it’s unlawful to make use of the darkish internet for legal functions or to acquire unlawful content material. It’s crucial to acknowledge that darknet browsers like Tor present dependable choices for sustaining anonymity.
Do Darknet Browsers Assure Full Anonymity?
By hiding IP addresses and sending site visitors by encrypted tunnels, darknet browsers like Tor supply a excessive stage of anonymity. Nonetheless, full anonymity remains to be unattainable. The will of intelligence companies to de-anonymize Tor customers highlights the need of taking strict safety measures.
Can Darknet Visitors Be Traced Again to Customers?
Layered encryption and IP masking by way of onion or garlic routing make it extraordinarily troublesome to hyperlink darkish internet actions to particular customers. Nonetheless, conditions together with firewalls, malware, of incorrect setups, or person error supplies a threat of identification disclosure. Superior worldwide foes may also compromise anonymity.
Can Regular Web sites Be Accessed By way of Darknet Browsers?
Sure, darknet browsers like Tor facilitate entry to common web websites. Nonetheless, as a result of IP masking, customers could seem to attach from a unique location, probably resulting in some websites making an attempt to dam Tor customers, limiting entry.
Are Darknets Impenetrable to Authorities Surveillance?
The NSA and different worldwide espionage organizations can’t fully keep away from the darknet. Nonetheless, with the adoption of strict security measures, sensible anonymity could be attained. As an alternative of being focused by refined opponents, Tor and different darknets shield customers from widespread surveillance.
What Are the Dangers Related to Darknet Looking?
The inherent dangers of utilizing the darkish internet embody being uncovered to viruses, identification theft, scams, and phone with illegal or immoral content material. Customers should be cautious in regards to the web sites they go to and the information they obtain. Moreover, deanonymization could also be attainable on account of browser flaws.
Conclusion
Darknet browsers present entry to the darkish internet and permit for nameless shopping. These browsers permit underrepresented teams to get pleasure from their proper to free expression, however in addition they carry the chance of cybercrime. Due to this fact, it’s essential to rigorously stability the advantages and disadvantages earlier than partaking in darkish internet exercise. Make the most of robust anonymity mechanisms and consider the moral and authorized repercussions to scale back dangers.
Disclaimer
Any information, textual content, or different content material on this web page is supplied as common market data and never as funding recommendation. Previous efficiency shouldn’t be essentially an indicator of future outcomes.
![]()
![]()
The Belief Undertaking is a worldwide group of stories organizations working to ascertain transparency requirements.
Damir is the group chief, product supervisor, and editor at Metaverse Submit, protecting subjects resembling AI/ML, AGI, LLMs, Metaverse, and Web3-related fields. His articles appeal to a large viewers of over one million customers each month. He seems to be an professional with 10 years of expertise in website positioning and digital advertising and marketing. Damir has been talked about in Mashable, Wired, Cointelegraph, The New Yorker, Inside.com, Entrepreneur, BeInCrypto, and different publications. He travels between the UAE, Turkey, Russia, and the CIS as a digital nomad. Damir earned a bachelor’s diploma in physics, which he believes has given him the crucial considering expertise wanted to achieve success within the ever-changing panorama of the web.
Extra articles

Damir is the group chief, product supervisor, and editor at Metaverse Submit, protecting subjects resembling AI/ML, AGI, LLMs, Metaverse, and Web3-related fields. His articles appeal to a large viewers of over one million customers each month. He seems to be an professional with 10 years of expertise in website positioning and digital advertising and marketing. Damir has been talked about in Mashable, Wired, Cointelegraph, The New Yorker, Inside.com, Entrepreneur, BeInCrypto, and different publications. He travels between the UAE, Turkey, Russia, and the CIS as a digital nomad. Damir earned a bachelor’s diploma in physics, which he believes has given him the crucial considering expertise wanted to achieve success within the ever-changing panorama of the web.
[ad_2]
Source link




