[ad_1]
The crypto group is grappling with points surrounding bug bounty packages, a vital mechanism for locating and addressing system vulnerabilities.
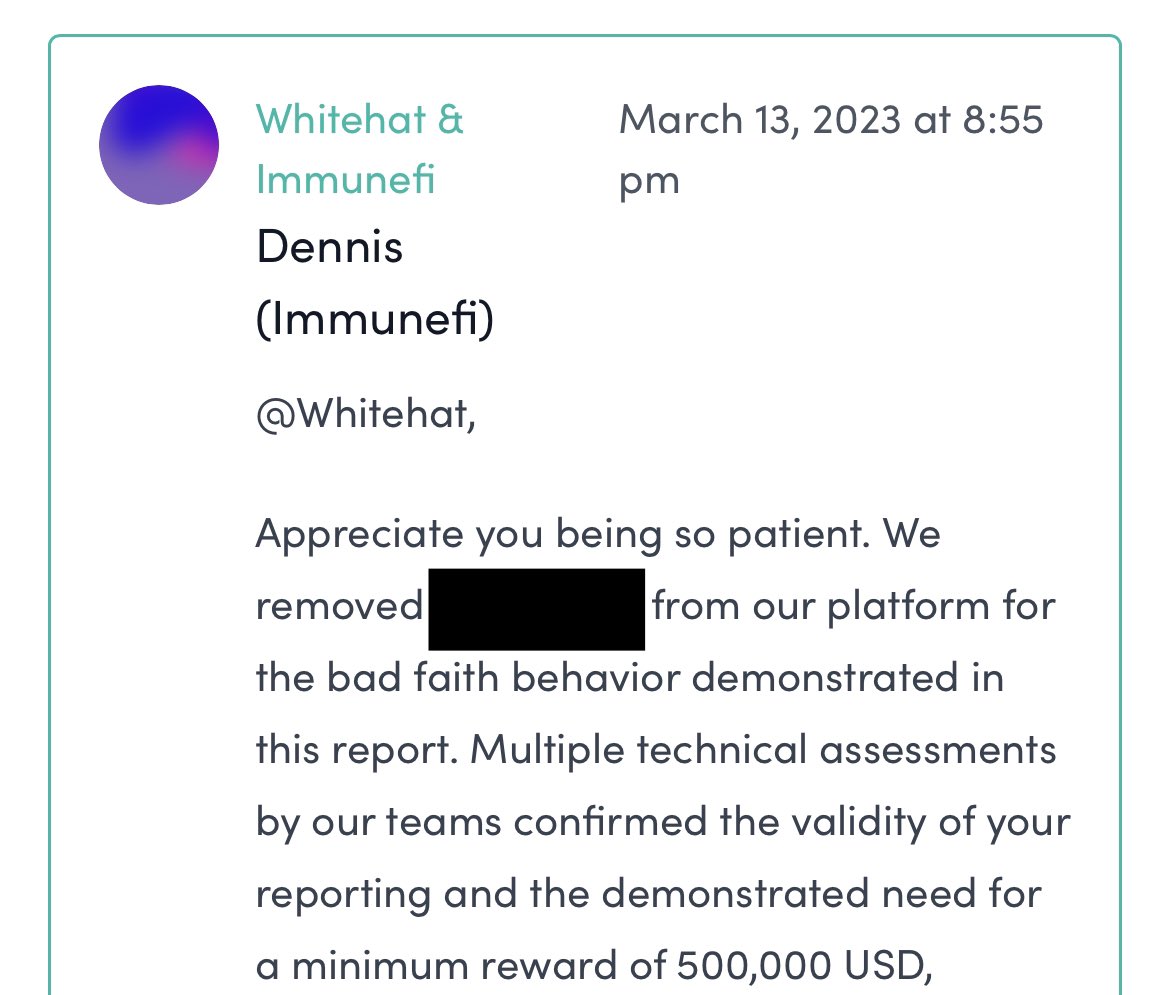
Usmann Khan, a web3 safety auditor, posted on Aug. 17, “Keep in mind that initiatives can merely not pay, whitehat,” with a screenshot of a message from Immunefi indicating a challenge had been faraway from its bug bounty downside for failure to pay a minimal of $500,000 in bounties.
In response, safety researcher Marc Weiss shared the ‘Bug Bounty Wall of Disgrace’ (BBWoS), a listing documenting unpaid rewards allegedly owed to white hat hackers in web3. The info from BBWoS seems to sign a major lack of accountability and belief inside the crypto ecosystem that can not be ignored.
The BBWoS signifies {that a} bug bounty for the Arbitrum exploit of Sep. 2022 had a $2 million reward. But, the white hate was awarded simply $780,000 for figuring out an exploit that uncovered over $680 million.
Additional, BBWoS states the CRV borrowing/lending exploit on Aave from Nov. 2022 led to the lack of $1.5 million, with $40 million in danger, and no bounty was paid to the white hat who recognized the assault path “days earlier than.”
Lastly, in April this yr, simply $500 was paid to a white hat who reportedly recognized a method for managers to steal as much as $14 million price of “tokens from customers utilizing malicious swap paths” after being advised by dHEDGE that the problem was “well-known.”
The listing was created by whitehat hackers “uninterested in spending sleepless nights discovering bugs in protocols solely to have a payout of $500 when the financial harm totals within the hundreds of thousands,” with the creator stating,
“I created this leaderboard to assist inform the safety group as to the initiatives that don’t take safety severely so we are able to keep away from them and spend time on the initiatives that do.”
The necessity for in-house auditors in DeFi.
In his presentation on the DeFi Safety Summit in July, Weiss highlighted auditors’ crucial position at numerous phases of protocol improvement. By integrating auditors and researchers in-house, he confused their potential to make insightful architectural selections, design efficient codebases, and undertake a security-focused strategy to protocol improvement.
Consequently, it’s regarding when platforms fail to acknowledge and adequately reward the efforts of those safety professionals when engaged on a contract foundation.
Auditors Gogo and MiloTruck highlighted that non-payment for recognized vulnerabilities is a widespread subject. Their posts underscore the pressing want for these platforms to reinforce their accountability and trustworthiness and guarantee due recognition for white hat hackers.
Extra transparency is required in dealing with vulnerabilities. Excessive-profile circumstances listed on BBWoS, just like the compromised deposit contract of Arbitrum, the financial exploit of Aave, and the malicious swap paths in dHEDGE, amplify this want.
Trusted Execution Environments in DeFi.
In response to Weiss’s points about belief, Danny Ki from Tremendous Protocol emphasised the potential of “decentralized confidential computing” to bolster belief in Web3 initiatives and mitigate vulnerabilities. Ki is referencing the choice to run DeFi in Trusted Execution Environments (TEE), one thing inherent in Tremendous Protocol.
A TEE is a safe space of a processor that ensures code and information loaded inside be protected for confidentiality and integrity. Nonetheless, one drawback of utilizing TEEs inside DeFi dApps is counting on proprietary structure from centralized corporations equivalent to Intel, AMD, and ARM. There are efforts within the open-source group to develop open requirements and implementations for TEE, equivalent to Open-TEE and OP-TEE initiatives.
Ki argues that ought to “Web3 initiatives function inside confidential enclaves, there could also be no must pay out for vulnerabilities, because the safety will likely be inherently fortified.”
Whereas a fusion of blockchain and confidential computing may present a formidable safety layer for future initiatives, the transfer to exchange bug bounties and safety auditors with TEEs appears complicated, to say the least.
Points with bug bounties in DeFi.
Nonetheless, there are further considerations for white hat hackers, equivalent to improper bug disclosures from safety companies on social media. A submit from Peckshield figuring out a bug in July merely stated, “Hello @JPEGd_69, it’s your decision to have a look,” with a hyperlink to an Ethereum transaction.
Gogo lambasted the submit stating, “If this vulnerability have been responsibly disclosed as an alternative of exploited, PEGd’s customers wouldn’t have misplaced $11 million, No reputational harm would have been precipitated, The man would have gotten a stable bug bounty as an alternative of been front-run by an MEV bot.”
Gogo shared their bug bounty expertise with Immunefi, an organization they described as ‘past improbable,’ the place the payout required a mediation course of, finally resulting in a passable payout of $5k for a crucial bug.
These insights from the web3 safety group underscore the crucial position of auditors and the significance of efficient bug bounty packages to the crypto ecosystem’s safety, belief, and development.
As some have recognized, hacks are lined extensively within the information and on X, however what for individuals who uncover the exploits and are by no means adequately compensated? Almost $2.5 million in allegedly unpaid bounties is listed on BBWoS alone, but, as Ki highlighted, may the long run embrace a web3 that’s innately safe without having for bounties?
[ad_2]
Source link



